Session Protection
Detect and block credential stuffing attacks in real time. VeriClouds CredVerify threat intelligence mitigates the risk of compromised credentials.
Traditional security systems do not continuously verify users during the typical 8-hour session. This gap leaves a vulnerability:
If a user's credentials are compromised during this time, the system does not recognize the breach and fails to terminate the session. Concurrently, organizations are frequently unaware when their employees' credentials are compromised, markedly increasing the risk of data breaches.
Recognizing this, Session Protection, powered by CredVerify, is designed to mitigate these vulnerabilities. It provides a comprehensive solution to protect user identities and sensitive data against evolving cyber threats.

The leading cause of data breaches remains constant
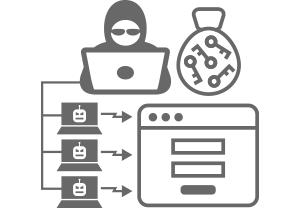
Credential stuffing
Credential stuffing remains a leading cause of data breaches due to the widespread reuse of passwords across multiple sites, making it easier for attackers to gain unauthorized access using stolen credentials.

Account takeover attacks
Account takeover attacks continue to be prevalent as they exploit weak or stolen credentials, often obtained through phishing or other forms of social engineering, allowing attackers to illicitly access and control user accounts.
Session replay
Session replay persists as a significant threat because it enables attackers to capture and retransmit the actions of a legitimate user, often bypassing traditional security measures by mimicking authentic user behavior.
Stop account takeover attacks before they begin
Protect your customer sessions now: prevent unauthorized access by threat actors and alert legitimate account holders of credential breaches in real time.
Forward thinking organizations can follow this path to ensure robust protection:
- Integrate: Seamlessly incorporate VeriClouds' CredVerify with the Shared Signals Framework (SSF) into your systems. This integration enables real-time detection of compromised credentials and enhances cybersecurity through automated monitoring.
- Remediate: Automatically address and neutralize identified security threats. By using the combined capabilities of CredVerify and SSF, this step involves immediate actions like resetting compromised credentials and blocking unauthorized access.
- Monitor: Continuously observe user activity and session integrity. This involves real-time surveillance to detect unusual behavior, signaling potential security breaches or compromised accounts.
- Respond: Develop and execute a rapid response to threats. This includes implementing security protocols such as password resets, account locks, and alerting both security teams and account owners for immediate action against any security compromise.


Elevate your cybersecurity with CredVerify and the Shared Signals Framework
The Shared Signals Framework (SSF) is designed to enhance online security and identity management. When integrated with CredVerify, it helps enterprises enable the following capabilities:
- Improved real-time threat detection: SSF enables organizations to detect and respond to security threats in real time. By sharing security signals across different platforms and services, it allows for quicker identification of suspicious activities, reducing the time between the occurrence of a threat and its detection.
- Enhanced coordination among service providers: This framework fosters better collaboration and information sharing among different service providers. When one service detects a security issue, such as a compromised account, it can send a signal to other services. This coordinated approach helps in mitigating risks more effectively across all platforms where the user has a presence.
- Continuous authentication and authorization: Traditional authentication methods often only verify user credentials at the login stage, failing to account for changes in user status or behavior during a session. The SSF supports continuous authentication, constantly monitoring and evaluating the security status of a session. This ensures that any change in the user's risk profile, such as a compromised account detected elsewhere, can trigger appropriate responses like re-authentication requests or session termination, thereby enhancing overall session security.
Powered by the VeriClouds Credential Threat Intelligence Platform
When you adopt SSF and the Session Protection solution based on the VeriClouds platform, you get the best of both worlds. This powerful combination automates detection and response to Account Takeover and credential stuffing, using advanced intelligence for real-time monitoring, ensuring superior defense against sophisticated cyber threats.
