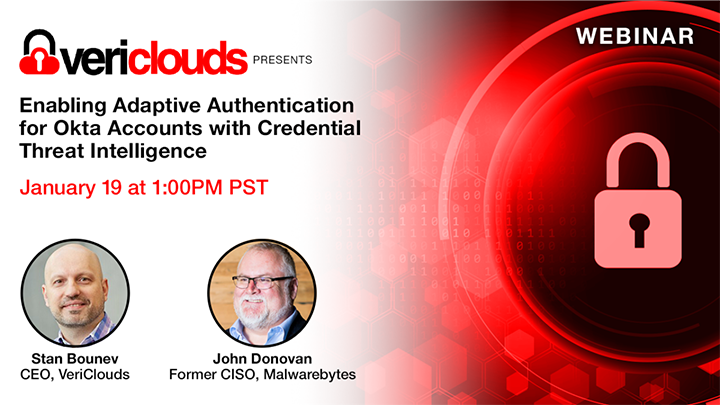

Stan Bounev
Founder & CEO
VeriClouds

John Donovan
Former CISO
Malwarebytes
If you’re an Okta customer and thinking about how to move your organization from contextual access to adaptive authentication, credential threat intelligence is the key.
Location blacklisting, IP reputation, and behavior detection are not sufficient anymore to distinguish the legitimate user from an attacker.
Threat intelligence helps organizations to move from contextual access to adaptive workforce on the Okta Zero Trust maturity curve. Risk-based access policies complement context-based policies to deliver real-time insight about the user.
In this webinar, we will explain how integration between the Okta authentication service and credential threat intelligence service can significantly lower the risk of unauthorized access by utilizing a fully automated process.
Access the recording below

